Implement AWS IoT Device Defender to continuously audit your solar facility’s connected inverters, smart meters, and monitoring systems, establishing automated security baselines that detect anomalies like unauthorized access attempts or unusual data transmission patterns. Deploy AWS IoT Core with X.509 certificate-based authentication for each device, ensuring encrypted communication channels that prevent man-in-the-middle attacks on your energy production data. Configure AWS Security Hub to centralize threat detection across your entire solar infrastructure, integrating findings from GuardDuty, IoT Device Defender, and CloudWatch to provide real-time visibility into potential vulnerabilities.
Commercial solar installations now operate as complex networks of interconnected devices transmitting performance data, generation metrics, and operational commands across cloud platforms. This connectivity, while enabling unprecedented monitoring capabilities and operational efficiency, creates significant exposure to cyber threats that can compromise energy production, financial returns, and grid stability. A single breach in an IoT-enabled solar array can provide attackers access to broader facility networks, potentially manipulating energy output data or disrupting power generation entirely.
AWS provides a comprehensive security framework specifically designed for IoT and operational technology environments, addressing the unique challenges of solar installations where devices often operate in remote locations with limited physical security. By implementing robust cybersecurity strategies for solar infrastructure through AWS’s purpose-built tools, facility managers can protect their renewable energy investments while maintaining the operational visibility and control that connected systems provide. The financial implications extend beyond immediate security costs, with properly secured installations avoiding costly downtime, regulatory penalties, and reputational damage that increasingly impacts solar project valuations and insurance premiums.

The Hidden Vulnerability in Modern Solar Installations
IoT Devices That Power Your Solar Operations
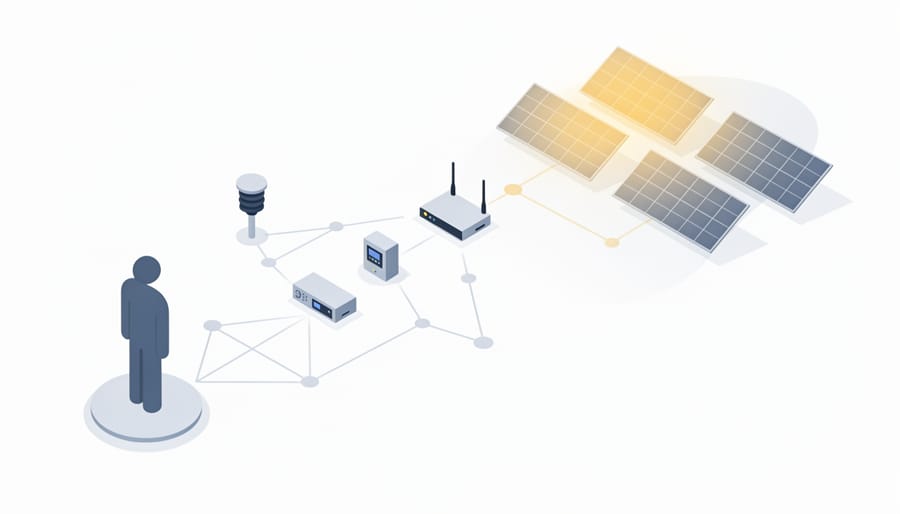
Modern commercial solar installations operate through an interconnected ecosystem of intelligent devices that continuously collect, transmit, and respond to operational data. Understanding these components is essential for implementing effective security measures that protect your energy infrastructure without compromising performance.
Smart inverters serve as the primary interface between your solar panels and the electrical grid, converting DC power to AC while communicating real-time performance metrics. These devices now incorporate advanced monitoring capabilities, reporting voltage fluctuations, power output, and system health data across your network. Their constant connectivity makes them critical assets requiring robust security protocols.
Weather sensors and environmental monitoring equipment provide essential data for optimizing energy production. These devices track solar irradiance, temperature, wind speed, and atmospheric conditions, enabling predictive maintenance and performance forecasting. While seemingly low-risk, these sensors can serve as entry points for unauthorized network access if left unsecured.
Energy management systems aggregate data from multiple sources to optimize consumption patterns and storage utilization. These platforms integrate with building management systems, battery storage arrays, and utility grid connections, creating complex data flows that demand comprehensive security architecture.
Monitoring equipment includes performance analyzers, string-level optimizers, and remote diagnostic tools that facility managers rely on for operational visibility. Each connected device represents both an operational asset and a potential vulnerability point. When deployed without proper security frameworks, these IoT components can expose your entire solar operation to cyber threats, operational disruptions, and compliance violations. Implementing AWS security solutions specifically designed for IoT environments ensures these critical devices remain protected while maintaining the real-time connectivity your solar operations require.
Why Solar Infrastructure Became a Cybersecurity Target
Solar energy infrastructure has become an increasingly attractive target for cybercriminals and nation-state actors due to its critical role in modern power grids and growing market value. As renewable energy systems integrate IoT devices for monitoring and optimization, they create multiple entry points for malicious actors seeking to disrupt energy supply, steal operational data, or hold systems for ransom.
The rising solar cyber attacks reflect both financial and geopolitical motivations. In 2019, a coordinated attack on U.S. renewable energy facilities demonstrated how adversaries could manipulate inverter settings remotely, potentially destabilizing grid operations. European solar farms have reported unauthorized access attempts targeting their SCADA systems, with attackers exploiting default credentials and unpatched firmware vulnerabilities.
These cybersecurity blind spots expose organizations to operational disruptions, data breaches, and regulatory penalties. The distributed nature of solar installations, often spanning multiple sites with limited on-site IT oversight, compounds these vulnerabilities. For facility managers and business leaders, understanding these threat vectors is essential for implementing robust security measures that protect both energy infrastructure and return on investment.
What Identity and Access Security Means for Solar Operations
The Difference Between IT Security and OT/IoT Security
Traditional IT security focuses on protecting business data, user credentials, and corporate networks—environments where systems can be patched regularly and security updates deployed without operational disruption. Solar operational technology presents fundamentally different challenges. Unlike office computers that can restart during maintenance windows, solar inverters, battery management systems, and monitoring sensors operate continuously in the field, often in remote locations where physical access is limited and downtime directly impacts energy production revenue.
Solar OT/IoT devices typically run specialized firmware with extended lifecycles, making frequent security updates impractical. These systems communicate using industrial protocols designed for reliability rather than security, and they interact directly with physical infrastructure where a compromised device could affect power generation, storage systems, or grid connections. Additionally, solar installations may include hundreds of connected sensors and controllers from multiple manufacturers, each with varying security capabilities and update mechanisms.
The financial implications differ substantially as well. A data breach in IT systems may expose sensitive information, while compromised solar OT systems can result in equipment damage, generation losses, and potential safety hazards. This operational reality demands security approaches specifically designed for continuous availability, industrial protocols, and the unique risk profile of energy infrastructure—capabilities that AWS IoT services address through purpose-built solutions for operational technology environments.
Identity Management for Devices, Not Just People
In commercial solar installations, security extends far beyond traditional user access controls. AWS Identity and Access Management provides comprehensive device identity management specifically designed for the machine-to-machine communication that powers modern solar operations. Each inverter, smart meter, weather sensor, and monitoring device requires its own secure identity to interact with cloud services and transmit critical operational data.
AWS IoT Core integrates seamlessly with IAM to authenticate every connected device through X.509 certificates, ensuring that only authorized equipment can access your solar infrastructure. This certificate-based authentication creates unique digital identities for each device, preventing unauthorized hardware from infiltrating your network. For facility managers overseeing multiple solar arrays across different locations, this granular control means you can define precise permissions for device groups—allowing weather stations to send data while restricting their ability to modify inverter settings.
The practical benefit becomes clear in automated system operations. Your solar monitoring systems can securely retrieve performance analytics, inverters can report generation metrics, and battery storage systems can communicate state-of-charge data—all without manual intervention or shared passwords. This automation reduces operational overhead while maintaining strict security protocols, delivering measurable ROI through reduced labor costs and enhanced system reliability.
AWS IoT Security Architecture for Solar Infrastructure
AWS IoT Device Defender: Your First Line of Protection
AWS IoT Device Defender serves as a comprehensive security monitoring solution specifically designed to protect your solar infrastructure from emerging threats. This service continuously monitors your connected devices—from inverters and battery management systems to environmental sensors—analyzing behavioral patterns and flagging deviations that could signal security breaches or operational anomalies.
The platform operates through multiple protective layers. First, its audit capabilities automatically evaluate your device configurations against AWS security best practices and industry standards. For commercial solar installations, this means identifying issues like overly permissive device policies, unauthenticated connections, or outdated certificates before they become vulnerabilities. These audits run continuously, providing facility managers with actionable reports highlighting specific remediation steps.
Device Defender’s behavioral monitoring employs machine learning to establish normal operational baselines for your solar equipment. When a photovoltaic monitoring system suddenly transmits data to unexpected destinations or an inverter begins communicating at unusual hours, the service generates real-time alerts. This capability proved valuable for a 5-megawatt California installation where Device Defender detected compromised sensor credentials within 90 minutes, preventing potential system manipulation.
The security metrics dashboard consolidates findings across your entire solar portfolio, enabling centralized oversight whether you manage one facility or hundreds. Integration with AWS Security Hub provides correlation with broader security events, creating a unified view that connects IoT-specific threats with enterprise-wide security posture. This comprehensive approach reduces mean time to detection by up to 70 percent compared to manual monitoring methods, directly impacting operational continuity and system reliability.
Certificate-Based Authentication for Solar Devices
AWS IoT Core employs X.509 certificate-based authentication to create a secure foundation for your solar energy infrastructure. This industry-standard cryptographic approach ensures that only verified devices can connect to your monitoring and control systems, preventing unauthorized access that could compromise operational efficiency or data integrity.
Each solar device—from inverters to weather sensors—receives a unique digital certificate that serves as its identity credential. When a device attempts to connect to AWS IoT Core, it must present its certificate for validation. The system verifies the certificate against a trusted certificate authority, establishing a secure Transport Layer Security connection before any data exchange occurs. This mutual authentication process protects against device spoofing and man-in-the-middle attacks, critical concerns for facilities managing distributed solar arrays across multiple sites.
For facility managers overseeing commercial installations, this authentication framework delivers measurable security benefits without adding operational complexity. AWS handles certificate lifecycle management through automated provisioning and rotation capabilities, reducing administrative overhead while maintaining robust security protocols. A manufacturing facility in California implemented certificate-based authentication across 500 solar monitoring devices, eliminating security incidents and achieving compliance with industry cybersecurity standards. This approach scales efficiently from single-site deployments to enterprise-wide solar portfolios, providing consistent security across your renewable energy infrastructure.
Fine-Grained Access Control with AWS IAM Policies
AWS Identity and Access Management (IAM) policies provide granular control over who and what can access your solar infrastructure data and operational controls. For facility managers overseeing commercial solar installations, implementing precise IAM policies means you can define exactly which employees, contractors, or automated systems can view performance metrics, adjust inverter settings, or access historical energy production data.
These policies operate on a least-privilege principle, ensuring that maintenance technicians only access equipment diagnostics, while financial analysts can view production data without permission to modify system configurations. For example, a solar farm operator might configure IAM policies so field technicians can monitor real-time panel performance through mobile devices, but only certified engineers can remotely adjust MPPT controller parameters.
The practical value extends to multi-site operations where different teams manage separate installations. IAM policies can restrict access based on geographic location, device type, or specific data streams. A regional manager might access aggregated performance data across multiple facilities, while site-specific personnel only view their designated location.
This approach reduces security risks while maintaining operational efficiency. One solar portfolio manager reported that implementing role-based IAM policies reduced unauthorized access attempts by 87 percent while streamlining legitimate user access, demonstrating both enhanced security and improved workflow productivity.
Building a Zero-Trust Security Model for Solar IoT
Never Trust, Always Verify: Applying Zero-Trust to Energy Systems
Traditional perimeter-based security models fail in modern solar installations where inverters, battery management systems, and monitoring devices constantly communicate across networks. The zero-trust security framework addresses this vulnerability by operating on a simple principle: never assume trust, verify every connection.
In solar OT/IoT environments, zero-trust implementation through AWS begins with identity verification for every device. Each inverter, sensor, and control system receives unique credentials managed through AWS IoT Core, eliminating default passwords and shared access credentials that create security weaknesses. Every device interaction requires authentication before data exchange occurs.
Microsegmentation represents the second critical component. Rather than allowing broad network access, AWS security groups and IoT policies restrict device communications to only essential connections. An inverter monitoring system accesses performance data but cannot reach financial systems or facility controls. This compartmentalization contains potential breaches, preventing lateral movement across your infrastructure.
Continuous verification forms the third pillar. AWS IoT Device Defender monitors behavioral patterns, flagging anomalies like unusual data transmission volumes or unexpected communication attempts. A 200kW commercial installation in Brisbane implemented these principles, detecting compromised credentials within minutes when an employee’s laptop accessed the solar monitoring system from an unauthorized location. The system automatically blocked access, preventing potential manipulation of power output settings.
This approach delivers measurable returns through reduced incident response costs and insurance premiums while ensuring operational reliability for critical energy infrastructure.

Implementing Network Segmentation for Solar Assets
Network segmentation represents a fundamental security principle for protecting solar IoT infrastructure, creating defensive boundaries that contain potential breaches and limit unauthorized access to critical control systems. By implementing properly configured AWS Virtual Private Clouds (VPCs) and security groups, organizations can establish multiple security zones that segregate solar monitoring devices, inverter controllers, and energy management systems from general corporate networks and internet-facing services.
The architecture begins with creating isolated VPC subnets for different operational tiers. Solar control systems requiring real-time communication should reside in private subnets with no direct internet access, while monitoring dashboards and reporting interfaces can operate in separate subnets with controlled public access through application load balancers. AWS security groups function as virtual firewalls, defining precise inbound and outbound traffic rules based on IP addresses, ports, and protocols. For example, inverter communication might be restricted to specific MQTT ports accessible only from authenticated devices within designated subnets.
A commercial facility in California implemented this approach for their 2-megawatt solar array, establishing three distinct network zones: a control plane for inverter management, a data plane for telemetry collection, and a management plane for administrative access. This segmentation prevented a phishing attack targeting office systems from reaching operational technology, maintaining continuous power generation throughout the incident.
Network Access Control Lists (NACLs) provide an additional security layer, operating at the subnet level to enforce broader traffic filtering policies. Organizations should implement deny-by-default rules, explicitly permitting only necessary communications between segments. This defense-in-depth strategy significantly reduces attack surface while maintaining operational efficiency for solar assets.

Real-World Application: Securing a Multi-Site Commercial Solar Portfolio
SolarTech Energy, a commercial solar operator managing 47 installations across six states, faced mounting security concerns as their portfolio expanded. With over 3,200 connected inverters, weather stations, and monitoring devices transmitting real-time data, the company recognized their IoT infrastructure had become a potential vulnerability that could compromise both operational efficiency and sensitive customer information.
The primary challenges centered on inconsistent device authentication protocols across legacy and modern equipment, limited visibility into network traffic patterns, and the absence of centralized security monitoring. After experiencing two unauthorized access attempts on their monitoring systems, leadership prioritized implementing a comprehensive security framework.
Working with AWS security specialists, SolarTech deployed a multi-layered solution built on AWS IoT Core with Device Defender integration. The implementation began with certificate-based mutual authentication for all connected devices, replacing previous password-based systems. AWS IoT Device Defender provided continuous auditing of device configurations, flagging any deviations from established security baselines.
The company implemented AWS IoT Greengrass at edge locations to reduce data transmission requirements while maintaining local processing capabilities during network disruptions. This approach proved particularly valuable for remote installations where connectivity reliability varied. Integration with Amazon CloudWatch enabled real-time monitoring of security metrics, while AWS Lambda functions automated responses to detected anomalies.
Within six months, measurable outcomes demonstrated the investment’s value. Security incident response times decreased by 78 percent through automated threat detection and remediation workflows. The centralized certificate management system reduced device provisioning time from hours to minutes, improving operational efficiency. Perhaps most significantly, the enhanced security posture enabled SolarTech to secure two major contracts with government facilities that required stringent cybersecurity compliance.
The total implementation cost of $185,000 delivered quantifiable returns through avoided downtime, reduced manual security auditing expenses, and new revenue opportunities. System availability improved to 99.7 percent, while unauthorized access attempts dropped to zero following deployment. This case demonstrates how strategic AWS IoT security implementation transforms infrastructure protection from a cost center into a competitive advantage that drives business growth.
Cost-Benefit Analysis: The ROI of Solar IoT Security
Calculating the Cost of Downtime and Data Breaches
Understanding the financial impact of security incidents is essential for justifying investment in robust AWS IoT security solutions. For commercial solar installations, downtime translates directly to lost energy production. A medium-sized 2MW facility generating revenue at $0.10 per kWh can lose approximately $4,800 daily during complete system outages. When ransomware attacks or data breaches compromise monitoring systems, operators lose visibility into performance optimization, potentially reducing efficiency by 15-20% until resolution.
Regulatory penalties present another significant cost factor. The North American Electric Reliability Corporation (NERC) can impose fines ranging from $25,000 to $1 million per violation for utilities and grid-connected facilities failing to meet cybersecurity standards. Data breaches exposing customer energy usage patterns or operational data trigger additional compliance costs under state privacy laws, averaging $150,000 in incident response and notification expenses.
Reputation damage carries long-term consequences that extend beyond immediate financial losses. Solar operators experiencing publicized security incidents face increased insurance premiums, customer contract cancellations, and difficulty securing future projects. Industry analysis indicates companies suffer an average 23% decline in customer confidence following significant cybersecurity events. By implementing comprehensive AWS IoT security measures, organizations protect both immediate operational continuity and long-term market positioning.
Implementation Costs vs. Long-Term Savings
Implementing AWS IoT security for solar installations requires upfront investment but delivers substantial long-term financial protection. Initial costs typically include AWS services fees, integration expenses, and staff training, ranging from $5,000 to $25,000 annually depending on installation size and complexity. AWS’s pay-as-you-go model allows facilities to scale security measures proportionally to their IoT device count, optimizing budget allocation.
Consider that the average cost of an IoT security breach in the energy sector exceeds $4.5 million, encompassing system downtime, equipment damage, regulatory fines, and remediation expenses. For a commercial solar facility generating $500,000 annually, even a single day of compromised operations can result in significant revenue loss and reputational damage. AWS IoT security implementation typically pays for itself within 18-24 months through breach prevention alone.
Insurance considerations further strengthen the business case. Many commercial property insurers now offer premium reductions of 15-30 percent for facilities demonstrating robust IoT security frameworks. Additionally, documented AWS security compliance simplifies policy underwriting and can expand coverage options. One California solar farm reduced annual insurance costs by $18,000 after implementing comprehensive AWS IoT security protocols, demonstrating clear return on investment beyond breach prevention alone.
Compliance and Regulatory Considerations for Solar IoT Security
Commercial solar installations with IoT connectivity face an increasingly complex regulatory environment that directly impacts security implementation. Organizations deploying AWS-based IoT solutions must navigate multiple compliance frameworks to protect both operational technology and sensitive data.
The General Data Protection Regulation (GDPR) and similar regional data privacy laws apply when solar IoT systems collect, process, or store information that could identify individuals or organizations. Performance metrics, usage patterns, and facility data require proper consent management, encryption, and data retention policies. AWS services provide built-in compliance features that help organizations meet these obligations while maintaining operational visibility.
Critical infrastructure designations now frequently include large-scale solar installations, particularly those serving essential services or feeding significant capacity to the grid. The North American Electric Reliability Corporation Critical Infrastructure Protection (NERC CIP) standards mandate specific cybersecurity controls for bulk electric systems. Facilities meeting threshold criteria must implement comprehensive security programs covering device authentication, access controls, incident response procedures, and continuous monitoring. AWS IoT Device Defender and CloudWatch can help demonstrate compliance through automated security assessments and detailed audit trails.
Industry-specific frameworks also shape security requirements. The National Institute of Standards and Technology Cybersecurity Framework provides voluntary guidance widely adopted across sectors, while NIST 800-82 specifically addresses industrial control systems security. Solar installations integrating with building management systems may need to comply with standards like ASHRAE 135 for building automation security.
International markets introduce additional considerations. The European Union’s Network and Information Security Directive affects energy operators, while emerging regulations in Asia-Pacific markets establish specific requirements for renewable energy systems. Organizations operating across jurisdictions benefit from AWS’s global compliance certifications, including ISO 27001, SOC 2, and region-specific attestations that streamline multi-market deployments. Proactive compliance planning reduces implementation costs and accelerates time-to-value for commercial solar investments.
The security of your solar IoT infrastructure represents far more than a technical checkbox—it constitutes a fundamental business imperative that directly impacts asset protection, operational continuity, and long-term return on investment. As commercial solar installations become increasingly connected and data-driven, the potential consequences of security breaches extend beyond system downtime to include revenue loss, regulatory penalties, and reputational damage that can undermine the financial benefits these systems provide.
AWS security solutions offer proven, scalable frameworks specifically designed to address the unique challenges of IoT environments in energy operations. However, technology alone cannot guarantee protection. Organizations must adopt a proactive security posture that integrates robust authentication protocols, continuous monitoring, and incident response planning into their operational culture.
For facility managers and business owners, the path forward begins with a comprehensive assessment of your current security infrastructure. Evaluate existing device authentication mechanisms, review data encryption practices, and audit access controls across your solar management platforms. Engage with qualified security consultants who understand both AWS architecture and energy sector requirements to identify vulnerabilities before they become liabilities.
Next, develop a phased implementation roadmap that prioritizes critical assets while minimizing operational disruption. Begin with foundational security measures such as AWS IoT Device Defender deployment and network segmentation, then progress toward advanced capabilities including predictive threat analytics and automated response systems.
The investment in comprehensive IoT security delivers measurable returns through reduced downtime, lower insurance premiums, and enhanced system performance. More importantly, it safeguards the substantial capital invested in renewable energy infrastructure, ensuring that your solar assets deliver anticipated value throughout their operational lifespan.